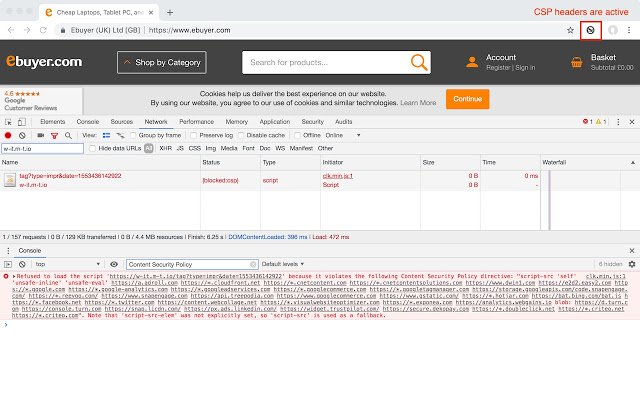
Use at your own risk. This disables the Content-Security-Policy header for a tab. Use this when testing what resources a new third-party tag includes onto the page.
Click the extension icon to disable Content-Security-Policy header for the tab. Click the extension icon again to re-enable Content-Security-Policy header.
Use this only as a last resort. Disabling Content-Security-Policy means disabling features designed to protect you from cross-site scripting. Prefer to use report-uri which instructs the browser to send CSP violations to a URI. That allows you keep Content-Security-Policy enabled in your browser but still know what got blocked. https://report-uri.com is a free tool that gives you a web interface to inspect CSP violations on your site.

暂时没有问题
Very good!
This doesn’t work in Chrome 87. It may have at somepoint in the past, but not now 🙁
I would like that whitelisting would be enabled! (I only want this for single domain)
UPDATE: it stopped working for me in late 2020 🙁
Solves the problem. It won’t automatically activate which is a plus on security.
Saved my life, great for development testing.
Doesn’t work. I tried this on JIRA Tempo TImesheets and didn’t work. CSP from app.tempo.io as still blocked.
Don’t know if it’s just me, but it seems it stopped working recently… It was working perfectly before.
It doesn’t work anymore on Chrome 80.0.3983.2. It shows “Provisional headers are shown” for external network call.
Thanks for uploading this! Simple. Does what it says. Registers a webRequest.onHeadersReceived listeners to clear the value of the CSP header. Exactly what I needed for development.
Working great for my office web.
牛逼!
Works! You have to click the button to activate it. I wish it had more options, like turn on, on a tab by tab basis, on a domain by domain basis, or just globally. currently only turns on/off globally, for all domains and tabs.
Working fine in April/2019.
Had issues while logging into an account. It says I have to verify captcha, but didn’t show me anything to click on, it was a blank field.
So I jumped on google, found this extension, was little worried if it’s scam and not doing what it’s should do but wow! that’s why I wrote this review. Super happy.
I installed it, gave it a try.
Had to click on its symbol in the plugin toolbar next to the url field.
Refreshed the tap and there we go!
Super happy, big thanks!
Not work.
It works fine for importing custom JS (Custom Javascript for Websites 2 is limited to 10KB script sizes so importing from a local server is often a requirement).
Also,
YOU NEED TO CLICK ON THE EXTENSION TO ENABLE.
It’s not on by default and I thought it wasn’t working -_-
не работает
Doesn’t work at all….
Intermittent success when using this extension but was a life saver for enabling me to pull data from a 3rd-party URL via a bookmarklet.
Did not find better way to bypass CSP set by HTML publisher in Jenkins.
fat
good job! THX
Didn’t work for me (Cordova)
太有用了,Diigo终于可以在zhihu这样的网站上面用了,👍
Worked